
The Politics of Cyber Attribution: Singapore’s Calculated Silence
Singapore’s decision to name UNC 3886, but not a state, is one of the more interesting cyber-signaling moves we’ve seen in Southeast Asia. Attribution is
Home / Archives for Gil Baram
Gil Baram’s blog about Cyber strategy and policy

Singapore’s decision to name UNC 3886, but not a state, is one of the more interesting cyber-signaling moves we’ve seen in Southeast Asia. Attribution is

In the current geo-strategic landscape, offensive cyber capabilities are essential to national security. So states are no longer debating whether offensive capabilities are necessary. They

Finland’s revised Cyber Security Strategy (2024-2035) introduced something new to Finnish cyber policy: a dedicated pillar for response and countermeasures. The strategy states explicitly that

Estonia’s approach to cybersecurity is shaped by direct experience. The 2007 cyberattacks on Estonian government, banking, and media websites — widely attributed to Russian actors
On March 6, the White House released “President Trump’s Cyber Strategy for America.” This 7-page document makes the most explicit case for offensive cyber operations

For most of its history, the EU approached cybersecurity as a regulatory and defensive challenge. NIS2, the Cyber Resilience Act, baseline hygiene. That era is

AI is reshaping military power, but most Professional Military Education institutions aren’t yet equipped to teach officers how to think critically about it. That’s the

I am very happy to see that our special issue about “Measurement and Meaning in the Study of Cyber Conflict” is finally out! This special

Last week, France published its National Cybersecurity Strategy for 2026-2030. The strategy defines cyberspace as a “theatre of power” and a field of operations where

Microsoft’s Digital Defense Report 2025 reinforces a shift many of us are already seeing in practice: today’s most damaging intrusions are less about exploiting systems

Navigating uncertainty in cyber conflict: incorporating false flags in the attribution process of offensive cyber operations *** False flags aren’t noise in cyber conflict. They’re

Last week, I had the privilege of speaking at the “Cyber Women Power” meeting, organized by The Israel Chamber of Information Technology – הלשכה לטכנולוגיות

Recently, I’ve read an interesting story that, in my opinion, highlights one of the greatest dangers we face as a society in the cyber-AI nexus:

It was great to be back in The Hague for the 2025 Conference on International Cyber Security, with the perfect title: “Order, disorder, re-order: Geopolitics

Today I had a great pleasure listening to a fascinating panel on the future of cyber diplomacy at the Singapore International Cyber Week. The panelists

Last week in Singapore, I had the privilege of leading our tabletop exercise as part of our AI-enabled cybercrime initiative. I am grateful to our

Last week in Prague, I had the privilege of speaking with the Czech Insurance Association about the intersection of cybersecurity, AI, and geopolitics — and

Last month, researchers reported an alarming metric: an AI pipeline that can generate validated, working exploits for published CVEs in approximately 10–15 minutes at an

Last Wednesday, I had the pleasure of speaking at Leiden University in The Hague, where I joined faculty and students for a seminar on the

OpenAI’s Disrupting Malicious Uses of AI: June 2025 report offers a revealing insight into how generative AI is being exploited through coordinated efforts by criminal

I have been studying cyber operations between countries for years, but what we have observed between Israel and Iran signifies a shift. These are not

This year, in my courses “Cyber Conflict and Strategy in a Changing World Order” (undergrad) and “Emerging Technologies and International Security – Cyber, AI, Space,

One last reflection from RSA Conference: I attended an inspiring and thought-provoking panel at RSA on Next Gen Cybersecurity Workforce. While listening, I thought everyone

Last week, I had the incredible honor of presenting my research, “The Dark Side of Innovation: How Nation-States Are Weaponizing AI in Cyberspace,” at the

A personal and professional highlight was participating in the panel “AI-enabled Cybercrime: Separating Hype from Reality” – where we shared insights from industry, policy, and

I recently read the in-depth analysis of Iran’s national strategy regarding AI by Recorded Future Insikt Group®. Despite facing economic and technological constraints, Iran is

What an engaging guest lecture we had in my undergraduate course, ‘Different Ways of Understanding Cyber Conflict: Cyber War, Intelligence Contest, or Strategic Competition?’. Last

Recent findings from Google’s Threat Intelligence Group (GTIG) highlight how government-backed actors utilize Gemini to enhance existing tactics, such as phishing, scripting, surveillance, and information

As part of my MA seminar, “Emerging Technologies and National Security, ” we hosted my dear friend and colleague, Refael Franco , as a guest speaker

I was honored to deliver a keynote presentation at AXA’s Chief Security Officer Forum in beautiful Cascais, focusing on the evolving landscape of AI-enabled cybercrime.

Earlier this week, I had the opportunity to speak on a panel exploring the growing cybersecurity threats to space systems. As our reliance on satellites

The Institute for Security and Technology (IST) ‘s latest report, “The Implications of AI in Cybersecurity: Shifting the Offense-Defense Balance,” explores how AI is reshaping

What an honor to be included in this list alongside such inspirational women! I am so proud and humbled to be recognized on the Cyber25

Last month, the World Economic Forum published its annual Global Cybersecurity Outlook, emphasizing important realities about the current cybersecurity landscape: rising cyber threats, changing tactics,

Recently, AI has been generating significant discussion, particularly regarding its implications for cybersecurity, cyberattacks, and cybercrime. Alongside our ongoing research at the University of California,

I recently wrote about the increasing risks of AI-driven cyber threats and their implications for security in Europe. Attackers are becoming smarter and might work

It was a great privilege to speak with the members of the special community founded by Sara Kop! Due to time constraints, we only discussed

I’m thrilled to share that I will be speaking at #RSAC 2025 Conference. Join us in San Francisco, April 28 – May 1, to add

Just before Christmas, we had a tabletop exercise (TTX) at UC Berkeley that brought together a group of the most talented experts in Silicon Valley

“Cyber Diplomacy through Official Public Attribution: Paving the Way for Global Norms” This time, I combine three of my favorite things – public attribution, data
It was such a pleasure discussing these two theories with my students.

Last week, I had the pleasure of speaking at the International Conference on Critical Infrastructure Systems in the AI Era in Belgrade. I (briefly) discussed

In 2020, I planned to attend my first in-person ISA conference in Hawaii. I had already booked my flight tickets, hotel, and volcano tour 🌋

Last week I attended RSAC for the first time. In one word – WOW! I listened to great panels and talks about the new cyber

Thank you so much, Kyla Guru, for joining us on Tuesday to discuss cyber education and share insights from your incredible journey! University of California,

Having the chance to chair a panel in a palace isn’t something I get to do every day 🙂 👑 As a matter of fact,

I had the pleasure of participating in a really interesting panel last week at the “Cyber Defending Taiwan” conference at UC Berkeley. My talk focused

Earlier this month I had a great time speaking at the American Political Science Association annual conference in Los Angeles on the intersection of Cyber
An interesting article recently published by the BBC addresses the question of why we rarely hear about cyber attacks carried out by Western countries. Before
Last week my new paper “Public Secrets: The Dynamics of Publicity and Secrecy in Offensive Cyber Operations” was published in the Journal of Global Security
In late May, the US State Department unveiled its groundbreaking strategic framework for space diplomacy. This strategy marks a significant shift, highlighting the State Department’s

Today I participated in the first Space Systems Command Artificial Intelligence/Machine Learning (AI/ML) Space Reverse Industry Day, which took place on the beautiful Microsoft Silicon Valley campus. Here are

Two weeks ago I had the privilege of being a part of an exceptional panel of international experts discussing the interconnection between space and cybersecurity,
Last week, I participated in an expert workshop on challenges in the cybersecurity of space systems. The goal of the workshop was to present and
So how secret are offensive cyber operations? In the past, offensive cyber operations have been covert: the results and repercussions of the offensive action have
US and UK officials announced last week that they had imposed sanctions on seven Russian citizens linked to Russian military intelligence. These citizens were involved

In the coming weeks, the US administration is expected to publish a strategy for the cyber security of critical national infrastructures. For the first time

There have been two interesting developments regarding the U.S. cyber command structure in recent months. I was interested in understanding what was going on as

Until not too long ago, offensive cyber operations were considered highly classified operations that were almost forbidden to talk about. An interesting quote from General
Last July, Albania experienced a series of cyberattacks that seriously damaged the proper functioning of the government services (I will write about the connection to

I am glad to share a new piece I wrote for The Lawfare Institute that discusses the available strategies for countries that suffered cyberattacks or intrusions. I

Iranian gas stations were disrupted across the country by a cyberattack last Tuesday. Gholamreza Jalali, the head of Iran’s Civil Defence Organization, stated: “We are

Yesterday I attended a fascinating discussion with CIA director William Burns at Stanford University. Director Burns described his plans in four key areas – 1.
On Thursday, many Israeli sites reported being hacked, their content replaced by messages calling for Israel’s destruction. Recently, Israel’s National Cyber Directorate warned of possible cyberattacks surrounding
A highly important source is The Cyber Vault Project, which is being built and maintained by researchers at George Washington University as part of a
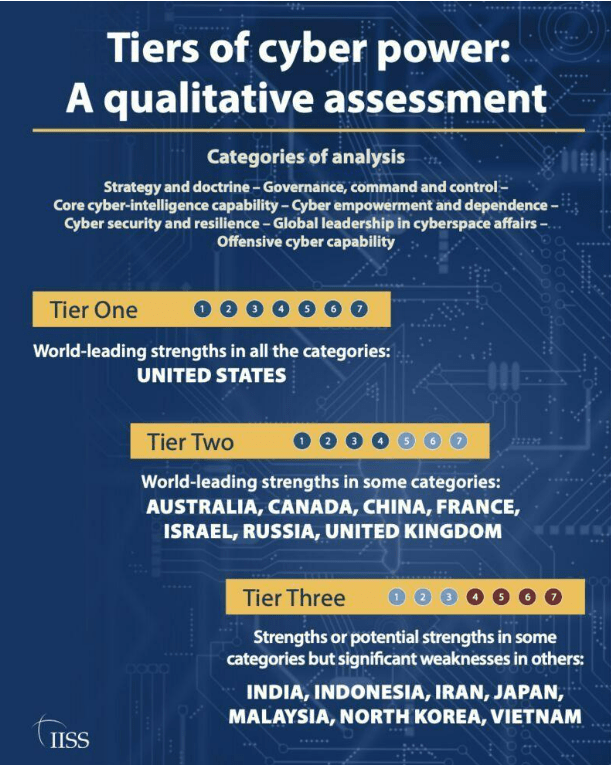
In recent years, we have heard a lot about ‘cyber power’ of countries, but when we think about what the term ‘cyber power’ means, there

Gen. Raymond: “Having a Space Force with a singular focus on the space domain will be hugely, hugely helpful to us [….] There’s a lot